Meta Quest: Attacker could make any Oculus user to follow (subscribe) him without any approval
Description
Attacker was able to subscribe any Oculus user on attacker's Oculus account without user approval. So it was possible to make very attractive account with a lot of real followers without their approval:). This followers are displayed in Oculus Quest device when you open user profile, also in profile opened in Meta Quest for Android and some other places.
Bug details
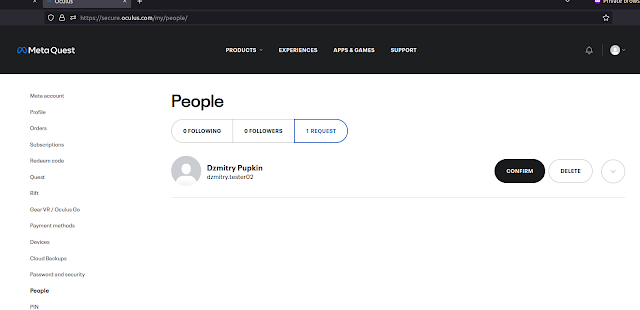
This page https://secure.oculus.com/my/people/ displays Oculus user followers:
If user (attacker) has enabled confirmation for follow requests, than everytime when somebody wants to follow him, user should confirm this action (see screenshot).
When user press "confirm" the next request is executed:
POST /graphql?locale=en_US HTTP/2
Host: graph.oculus.com
User-Agent: Mozilla/5.0 (X11; Ubuntu; Linux x86_64; rv:107.0) Gecko/20100101 Firefox/107.0
Accept: */*
Accept-Language: en-US,en;q=0.5
Accept-Encoding: gzip, deflate
Referer: https://secure.oculus.com/
Content-Type: application/x-www-form-urlencoded
X-Fb-Friendly-Name: OCAccountFollowRequestButtonsAcceptMutation
Content-Length: 1149
Origin: https://secure.oculus.com
Dnt: 1
Sec-Fetch-Dest: empty
Sec-Fetch-Mode: cors
Sec-Fetch-Site: same-site
Te: trailers
Where "follow_requester_id%22%3A%22109035146728YYY" represents parameter with Oculus ID who wants to follow user (your account). Now replace "109035146728YYY" on any other valid "XXXXX" Oculus ID and execute this request.
User "XXXXX" will be subscribed on your account (will follow you without any approvals from "XXXXX" side).
Timeline
23.11.2022: me: bug submited like issue found in People for Oculus Quest device app (I did't knew http request for this, but it worked via People app bug)
23.11.2022: me: found vulnerable request via https://secure.oculus.com/my/people/ page and have submited more details
24.11.2022: fb: triaged
26.11.2022: fb: reward $863 (750 + 113 bonus)
26.11.2022: me: asked to explain reward amount
30.11.2022: me: payment dispute
07.12.2022: fb: fixed
14.12.2022: fb: additional reward $863 (750 + 113 bonus) - total reward $1500 + $226 bonus
however I expected that this issue will have more impact than it was rewarded:), but ok.